What is a Digital Signature?
kevin.gray
Digital documents have become a go-to for many companies looking to streamline costs associated with managing paper documents. That means it’s more important than ever for businesses to make sure these items don’t get tampered with as they move back and forth between signatories.
Any alterations or unsanctioned access to an electronic document could lead to a data breach or other dire consequences. That’s why we wanted to highlight the role digital signatures play in making sure electronic records move securely between only those authorized to read the contents.
What is a Digital Signature?
The online signature represents the process of encoding a document with encryption and other security methods to prevent tampering. It’s done through a calculated computer process called an algorithm. Adding a digital signature prevents anyone other than the authorized recipient from viewing a document. Digital signatures designate an authorized signee for a specific document, acting as sort of a “fingerprint” for a transaction, guaranteeing the authenticity of the person signing a document.
How Does a Digital Signature Work?
Digital signatures resemble a handwritten signature in that each one is different for every signer. Companies that provide digital signature solutions typically comply with a set of requirements called the Public Key Infrastructure (PKI). It outlines the criteria on how businesses should implement electronic signature technology.
A provider’s algorithm must produce two sets of long numbers called a private key and a public key. The private key encrypts the document and ensures no one else can view the contacts. The public key confirms a match to a private key before decrypting a document.
Here’s a simple example of how the digital signature process might work for a manufacturing business getting ready to send a contract out to a vendor using eSignature software.
- The business user finalizes their document changes and sends the document to their vendor contact for a signature.
- The vendor contact receives the document and signs it.
- The eSignature software generates a private key matched to the vendor contact’s signature.
- The business user receives the signed document back along with a copy of the vendor contact’s public key. They will be able to open the contents of the document if there’s a direct match to the vendor contact’s private key.
- An inaccurate match between a public and private key means the document has been tampered with, making the signature on the current form invalid.
- If there’s a match, the business user will be able to the signed document and confirm its validity.
Why Use Digital Signatures?
Digital signatures represent one of the most critical components of an eSignature platform. They’re used to drive the security around and support the legal validity of an electronic signature. Digital signatures enact protection around an electronic signature from the moment it’s signed. Using digital signatures also increases the transparency of online transactions between businesses, customers, and vendors.
Another reason to use digital signatures is that they embed electronic signatures with a watermark that tracks changes. It’s also used to verify the completion of an online transaction and seals a file once it’s received the required electronic signature.
How Do You Create a Digital Signature?
The process of adding a digital signature to forms depends on a user’s choice of software. For example, when you add a signature line to a Word or Excel document, users can embed select an option from the menu that allows them to add information unique to the recipient.
It works similarly when users work with software from a digital transaction management (DTM) company, who function as a certificate authority for issuing digital certificates. They select an option from the menu to add a digital signature for each recipient of the document. Remember, digital signatures are completely different from adding an electronic signature to a record. You can learn more about the specifics of electronic signatures here.
Companies can also opt to issue self-signed digital certificates. However, recipients will not have the ability to verify its authenticity. They will be forced to use their judgment on whether to accept the digital certificate and provide an electronic signature. Using a self-signed digital certificate could lead to problems if a contract or other agreement end up challenged in court. It’s the reason most companies choose to use eSignature platforms from DTM companies that allow them to easily embed digital signatures into a document.
What’s the Difference Between a Digital Signature and an Electronic Signature?
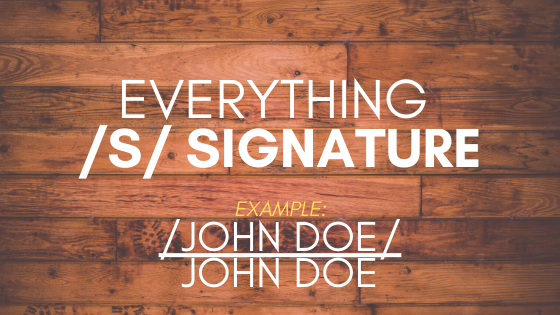
Electronic signatures serve as an acknowledgment that the signee accepts the terms of an agreement through electronic means. That includes typing their name in an email, entering a PIN into an ATM, signing their name electronically on a touch screen device, or selecting a checkbox to sign up for a new streaming subscription.
Digital signatures are created by platforms, like eSignature software, using a mathematical algorithm generated by a computer. They verify the identity of the person signing the document and validate the authenticity of an electronic signature. For more on the difference between digital and electronic signatures read here.
The Ins and Outs of Digital Signatures
Here’s a detailed rundown of the various components involved in creating and securing digital signatures.
- Hash Function — The hash represents the set of numbers and letters generated from an algorithm used by electronic signature software that is unique to a document. Hash functions are useful because they’re built to be one-way, meaning they can’t be reversed to find other files using the same values.
- Pubic key cryptology — Represents the cryptographic method used for generating the set of public and private keys associated with a document.
- Public key infrastructure (PKI) — PKI represents the standards, policies, people, and systems that offer support for distributing public keys and validating the identities of individuals or entities using a certificate authority and digital certificates.
- Certificate Authority (CA) — A trusted third-party charged with validating a signee’s identity. They also create the public/private key pair for someone or tie an existing public key from an individual back to themselves. After validating an identity, a CA provides them with a signed digital certificate. That information can then be used to verify the identity of a person tied to a public key.
Pretty Good Privacy (PGP)/Open PGP
PGP/Open PGP is an alternative to PKI which functions on the principle of the “Web of Trust.” Users offer trust to other users by signing the digital certificates of those with verified identities. The interconnection of the various signatures raises the likelihood of validating the identity of an individual on the internet.
What is a Digital Certificate?
Digital certificates function similarly to drivers licenses in that they verify the identity of the person presenting the information.
Digital Signature Certificate Classes
- Class 1 — Covers certificates issued to individuals and private subscribers. They confirm the details of a user name or email address. It’s the most basic digital signature certificate available.
- Class 2 — Covers certificates issued for use by business personal and private individuals. They confirm that the information provided in an application from a subscriber contains no conflicts with the information contained in a provider’s database.
- Class 3 — Covers high-assurance certificates issued to individuals and organizations primarily for e-commerce applications. They’re issued when a person presents themselves physically in front of a Certifying Authority.
Digital Signature Types
- Simple — Simple digital signatures do not use any encryption. Examples of simple signatures include wet signatures scanned in and placed into a document or typing out our signature at the end of an email.
- Basic — Basic digital signatures differ from simple signatures in that they show any changes that happen to a document once it’s been signed. However, it doesn’t validate the identity of a signee, which means they don’t carry much legal weight.
- Advanced and Qualified — Advanced and Qualified signatures carry the same legal validity as signing a paper document with a pen. They’re created using PKI and asymmetric cryptography technology. They track details like when a document was signed, where the person was, and the device that was used to create the electronic signature. It also traces any changes made to a document after receiving a signature.
One of the reasons that Advanced and Qualified signatures carry so much legal weight is the process used to verify a user’s identity. They rely on various methods of two-factor authentication before allowing a recipient to apply an electronic signature to a document, including:
- Asking recipients to enter a code sent to a mobile device
- Using biometric scanning on a mobile device
- Entering a one-time password sent through SMS
Digital Signature Uses
Digital signatures help electronic documents hold up in a court of law when there are legal challenges to the authenticity of an electronic signature. They help prove who signed a document, the time they signed, and the validity of the credentials. Digital signatures often prove essential in tracking the lifecycle of a document throughout the electronic signature process.